To somebody who has never owned or made his living creating and licensing intellectual property, it may not be a big deal.
 Really, who is it going to hurt when someone downloads a piece of software without paying for it and uses it for personal gain? Or, what’s the harm when a kid downloads music without paying for it. So what if I steal movies online, who gets hurt?
Really, who is it going to hurt when someone downloads a piece of software without paying for it and uses it for personal gain? Or, what’s the harm when a kid downloads music without paying for it. So what if I steal movies online, who gets hurt?
Ask the guy who bought the $1,200 graphics program for $89 from a faceless, nameless Internet pirate and he’ll likely tell you that the big software company has plenty of money and it charges too much for its stuff anyway.
But to a company like Adobe, that has spent millions in developing its suites of highly regarded programs, it is a big deal. It is lost revenue that rightfully belongs to the owners of the company. In many cases, that ownership is citizen stockholders, who are our neighbors and friends. It is also lost revenue that can be used in research and development of more and better software. And it raises the price of the software the rest of us buy.
Here is a very startling statistic, according to Business Software Alliance (BSA), 21% of software installed on personal computers is pirated. That fact alone could tell us why Adobe’s Dream weaver, for example, is listed at $700 instead of, say, $400. It is also one reason why upgrades are relatively cheap: The company is fairly certain they are dealing with a licensed software owner when they sell an upgrade, and the savings get passed on.
Hordes of software pirates
BSA, a Washington D.C.-based consortium of software and computer producers, has become the frontline of defense against the onslaught of hordes of pirates, who trade in, and use, pirated or illegal software. Given the tide against which the BSA swims, it may seem a bit like a great exercise in Quixoite-esque windmill jousting. Everybody does it, even people who otherwise seems like the moral pillars of the community.
BSA was formed in the late 90s by a group of software companies who realized that the threat to their industry was real. Their ability to engineer and produce programs for personal computers far outstripped their ability to protect their investment and intellectual property. Last year alone, companies like Adobe, Microsoft, Sun, Apple, Cisco, Dell and many more saw more than $7 billion in revenues siphoned off by pirates – and that’s just what they think they know about, the real numbers maybe much larger.
Rodger Correa, a spokesman for BSA, minces no words about the havoc software piracy wreaks on an industry which has nothing to sell but lines of code that get loaded onto computers.
“Not too many people really realize the incredible damage that is done to the industry by software piracy. They don’t realize it has a strong potential to undermine creativity and innovation in the marketplace,” Correa says. “It is a huge threat to the health of our industry.”
The copyright and licensing laws that cover software, as intellectual property, are pretty much the same as those covering music, publications, art and so on. Unfortunately, many folks do not understand the gravity of the situation.
Software versus a laptop
“Many people don’t really put a value on their software because they see it as intangible (this is especially true of software downloaded and not purchased as a set of discs in a box.) Most people would not go into an office and pick up someone’s laptop and leave. They know that is stealing. But they willingly take and use software that they haven’t paid for, I think because they don’t understand the value.”
In attempting to reverse this thinking and catch the bad guys who know they are stealing for profit, BSA has several weapons in its arsenal. The two most visible and most effective are education and enforcement. Enforcement is the one of which most folks are aware.
“We have our enforcement branch that tries to identify those companies, which may not be in compliance. We work with the government and the Justice Department, we do lots of monitoring of the Internet and we take reports of piracy from the general public.”
Those radio ads you hear around the country talking about software piracy and offering a reward for anyone who leads the BSA to a pirate have been an effective tool in bringing more companies, even major companies, into compliance.
It seems that, contrary to the popular image of software pirates being nerds in low places stealing cyberware from anyone they can, the biggest offenders are small, medium and large companies, who routinely violate copyright law, some knowingly and some not so willingly.
While enforcement gets the headlines for BSA, Correa says that is really only a small part of what they do and that the more important aspects are education and public relations.
If it sounds to good to be true – it isn’t
Correa says, “Education, for us, is helping the general public understand what intellectual property is and why it is important to protect it, in our case protecting our software property. But another big part of education is making people aware of the risks of dealing with software pirates.”
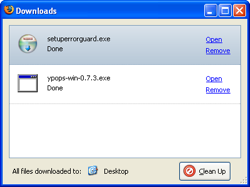
That $79 piece of pirated software may cost the end user far more in other expenses than the price of a legal program version. Aside from having to deal with fines and jail, if caught using it, users of pirated software face other dangers.
“We have examined thousands of pieces of illegal software offered in the Internet and in almost every case the pirated programs also contained spyware, viruses and other dangerous applications,” Correa explains.
Put a software title into a search engine and you almost certainly will get returns that include your item offered at a price that is far below the normal market. Correa says if it sounds to good to be true, probably is.
“We tell people to be very careful about where they buy and from whom they download. If it sounds to good to be true, it is probably a lie. Some people just get tricked though. One of the things we’re working on right now is online auctions. We found a number of trouble spots. We tell people that they need to make sure that the people they deal with when they download are reputable. Check the privacy statement details, check the background of the company, look for a Better Business Bureau, or PCI compliance seal. But sometimes price really does drive the deal and then people find themselves with bucked copies or they find their computer has been taken over by spyware or malware, and they become victims of identity theft,” Correa says.
Over or under licensed
BSA came up with a nice euphemism to refer to software thievery. They call it “under licensing.” It sounds better when the investigator thinks there is theft to suggest the business owner is under licensed and needs to come into compliance rather than accusing him or her of stealing.
Software theft or piracy happens a lot in companies that have more than one computer, sometimes by design and sometimes without the knowledge of the ownership. The common scenario is, company owns a copy of a program. The licensing agreement, which almost nobody ever reads, says it is to be used on one machine (many allow use on one portable machine as well). However, that one copy of, say, MS Office, winds up populating several machines. You can’t do that, that is an under licensed situation—that is theft of intellectual property.
Another scenario is where an employee uses a company machine to download pirated programs without the knowledge of the owner. The program then gets used for the good of the company (or not). The fact remains it is on premise and it remains illegally procured property and a liability to that company.
Either way the company and its management and ownership are liable for that theft. One of the BSA educational tools is helping business owners get into and/or stay in compliance in the licensing of their intellectual properties.
“Software asset management” is the key
Not everybody is under licensed.
“We do come across companies who have go to the extreme the other way and they are spending way too much on software licensing. We tell them they can do away with some of the expenses,” Correa says.
So how does someone know what their license liability is, especially if they have multiple machines with many software packages? There is a tool.
“We suggest something called ‘software asset management,’” Correa says. “The initial process can be automatic. BSA has tools that a manager can use to conduct audits of his company. Once audits are conducted then there needs to be a comprehensive and ongoing asset management program, which in the early periods can end up saving the company more money.”
Conducting the audit is the first step. The free downloadable tool can automate the process of finding out exactly what you have on your machine(s). Once you know you can check that against licenses you have. You may find that you are over licensed and can cut some costs immediately. If you are under licensed and wish to continue using the software it is time to contact a reputable vendor and buy the license.
“If you have questions or are not sure about a given situation, contact the licensor and discuss the matter. If you are trying to comply and you contact vendor they will do everything they can to help you,” Correa says.
Correa says folks shouldn’t feel threatened by calling BSA to ask about licensing issues. “If someone calls and they want to ask questions about their situation, they are not added to a target list or anything like them, we don’t do business that way. We’re more about helping people come into compliance and understand what it means and why it is important. That’s why we have provided the tools and education first and enforcement methods second.”
To be sure, BSA has prosecuted some bad guys and has been active in obtaining some serious settlement cash for their vendor members. The people that get caught face fines, settlements or, in some cases, criminal prosecution.
Implementing software asset management
Here are tips to implement a software asset management program:
- Step 1: Audit every computer in the company using the free tools at BSA.
- Step 2: Completely remove any software not being used or not approved by company
- Step 3: Completely remove any unlicensed software, which you do not intend to use.
- Step 4: If there is unlicensed software being used purchase rights immediately
- Step 5: Setup a three ring binder for each machine containing all licenses and original program discs for software on that machine.
- Step 6: Binder is kept in secure location to be checked out when needed.
- Step 7: Once every six months run an audit on each machine comparing it to what is in the binder.
- Step 8: Make adjustments for compliance if needed.
- Step 9: Deal with employees to abuse intellectual property