Purchases made with stolen payment cards cost the ecommerce industry billions of dollars a year worldwide. But, in at least some cases, merchants could have avoided losses had they recognized the telltale signs of fraud.
Fraudulent ecommerce orders typically fall into two categories.
- Friendly fraud is when a customer places an order with her own payment card, receives the goods ordered, but then calls her payment card provider and claims she never received the merchandise.
- Identity theft fraud happens when criminals place orders using stolen payment card information, often shipping the goods to freight forwarders.
In this article, I’ll focus on identity theft fraud since it is more common.
A LexisNexis Risk Solutions report published in October 2017 found that for 1,196 businesses surveyed — including 653 brick-and-mortar retailers and 190 ecommerce sellers — up to 43 percent of monthly transaction attempts (including declined or otherwise failed orders) involved fraud.
If these findings are not bad enough, LexisNexis also reported that when criminals use stolen credit cards (excluding stolen debit cards) to place ecommerce orders, those criminals are successful about 60 percent of the time.
Knowing how to recognize this form of payment card fraud could protect ecommerce businesses against significant losses.
7 Signs of Payment Card Fraud
Billing address vs. IP. An internet protocol address can be used to identify devices on the internet. While an IP address is not as accurate as a fingerprint, for example, it can give your business an idea of where a user is located.
If a shopper’s IP address is from, say, Sao Paulo, Brazil, but the billing address for the payment card is in Seattle, Wash., U.S., the purchase could be fraudulent, and probably requires at least a phone call or email message to verify the order.
Multiple purchases. Receiving many orders or nearly simultaneous orders from the same IP address can also be an indication of fraud.
In fact, identity theft fraud is particularly likely if all of the orders from this same IP address use different payment cards, different customer names, and different billing addresses.
High order velocity. From an analysis of fraudulent orders, payment provider Stripe learned that unusual order velocity was a strong indicator of payment card fraud.
This order velocity could take a couple of forms. For example, Stripe found that fraudulent orders did not follow normal buying behavior during the holidays.
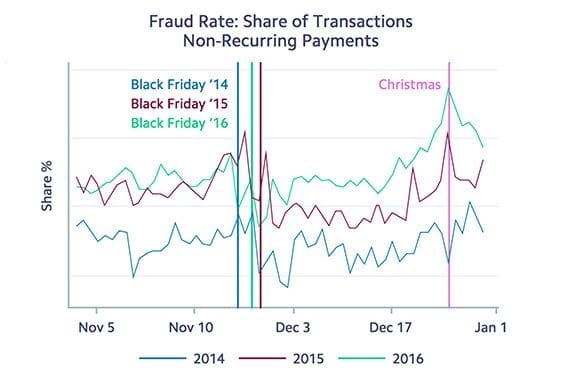
Stripe data showed that the dollar volume of fraud activity is somewhat consistent throughout the holiday season. As a percentage, it is relatively low on peak selling days, such as Black Friday, but relatively high during quiet times, such as Christmas Day.
The rate of fraudulent orders in Stipe’s analysis did not rise during peak shopping days, such as Black Friday, but it was unusually high as a percentage of total orders during otherwise quiet times, such as Christmas Day.
Thus, orders placed on Christmas, as an example, may merit more scrutiny than orders on Cyber Monday.
Similarly, Stripe noted that while the volume of orders goes down between midnight and 5 a.m. every day of the week, fraudulent activity as a percentage of total transactions increases during those hours.
Finally, an increase in fraudulent order velocity is often focused on a single item. Recently, in fact, the ecommerce business I manage was the victim of this type of payment fraud.
The business received two orders for an electric grease gun used for heavy equipment and tractors. Two orders in a single day was a lot, but the orders had none of the other signs of fraud. Once the shipping confirmations were sent for those two orders, however, five more orders for grease guns came in an hour. It turned out that all seven orders were fraudulent.
Failed card verification. Some payment processors and gateways allow merchants to set risk filters. And some sellers, often small businesses trying to get more orders, will unwisely set a low bar for card verification.
This can be a serious mistake since card verification failures, such as an incorrect card verification code (CVC), may be a strong indicator of fraud.
Failed address verification. The address verification system (AVS) allows merchants to compare the billing address a shopper provides to the billing address on file at credit card providers, such as Visa.
When a transaction fails to pass the AVS, it may be an indication of payment card fraud.
The AVS check is frequently done by the payment processor or gateway. But the decision to decline the transaction as a result of a failed AVS is often up to the seller.
Bad address. Criminals using stolen payment cards may make mistakes when submitting address information or may simply use fake information to place an ecommerce order.
Examples include the wrong zip code for the billing address, an incorrect area code for the phone number, or an email address that looks randomly generated. If the address and contact information is wrong, follow up.
Expedited shipping. Some criminals will try to create a sense of urgency by requesting next day shipping or similar — even when that shipping is very expensive relative to the value of an order.
Disproportionately high shipping costs can be an indication of fraud, and almost certainly merit further steps.
Similarly, be leery of orders with expedited shipping wherein the billing address and shipping address are not the same.