October is National Cyber Security Awareness Month. For small and mid-sized businesses, it’s a good time to strengthen a security plan with some free or relatively inexpensive tools and resources.
Here is a list of online security tools for small businesses. There are tools for backup storage, safe browsing, password management, network scanning, and combatting ransomware and distributed denial of service attacks.
Online Security Tools
Tor Project. Tor software protects you by bouncing your communications around a distributed network of relays run by volunteers all around the world. It prevents somebody watching your Internet connection from knowing the sites you visit or your physical location, and it lets you access sites that are blocked. Its free tools include a desktop browser and a proxy app for an Android device.
Qualys FreeScan. Qualys FreeScan service helps you to safely and accurately scan your network for security threats and vulnerabilities. FreeScan is limited to 10 unique security scans of Internet accessible assets. FreeScan provides a detailed report that can be used to correct and fix security threats proactively.
Samurai Web Testing Framework. The Samurai Web Testing Framework is a virtual machine, supported on VirtualBox and VMWare, that has been pre-configured to function as a web penetration environment for testing applications.
Open Threat Exchange. Open Threat Exchange, hosted by AlienVault, is an open threat information network. It provides real-time, actionable information for all participants. AlienVault also offers a free Reputation Monitor Alert, a service that alerts you whenever your public IPs and domains appear in the threat exchange network, indicating they could be compromised.
HTTPS Everywhere. HTTPS Everywhere is a Firefox, Chrome, and Opera extension that encrypts your communications with many major websites, making your browsing more secure. HTTPS Everywhere is a collaboration between The Tor Project and the Electronic Frontier Foundation.
Social-Engineer.com. Social-Engineer.com specializes in the art and science of social engineering. Social tactics are a growing trend in digital security, in the forms of phishing, phone elicitation, or impersonation. With Social-Engineer.com, you can learn how to protect against an attack to influence and manipulate people to gain physical access or access to vital information.
DuckDuckGo. DuckDuckGo is an Internet search engine that doesn’t store your search history or sell your information to advertisers that track you across the web. DuckDuckGo avoids personalized search results. Instead, it focuses on returning the best results, generated from hundreds of individual sources, including other search engines, such as Bing and Yahoo.
LastPass. LastPass is a password manager. Once you save a password in LastPass, you’ll always have it when you need it. When you’re ready to make a purchase, your profile will fill all your payment and shipping details for you. The built-in password generator creates long, randomized passwords that protect against hacking. LastPass is free, but also has a premium plan with encrypted file storage.
Ghostery. Ghostery is a browser extension that helps you manage website trackers for a safer experience. Ghostery detects and blocks tracking technologies to speed up page loads, eliminate clutter, and protect your data.
Comodo. Comodo One is a free remote monitoring and management, patch management, and service desk platform. Comodo also offers free and paid SSL certificates and an all-in-one advanced endpoint solution that runs all unknown files in a lightweight virtual container where they can be used safely and analyzed automatically.
StaySafeOnline.org. StaySafeOnline.org is powered by the National Cyber Security Alliance. It provides a list of free online security checkup tools and resources to learn how to protect yourself online. Get helpful resources from the N.C.S.A.’s sponsors and partners.
NSFocus. NSFocus protects customers and infrastructure from distributed denial of service attacks. Its products include Anti-DDoS System, Cloud DDoS Protection Service, and Threat Intelligence Subscription Service.
SpiderOak. SpiderOak is a storage service that’s focused on security. SpiderOak protects your group messaging, file sharing, and file backups with end-to-end encryption to keep you safe from privacy intrusions, ransomware, and data loss. Plans start at $5 per month.
ProtonMail. ProtonMail is an email service designed around security. All emails are secured automatically with end-to-end encryption. As a result, your encrypted emails cannot be shared with third parties. No personal information is required to create your secure email account. There are no IP logs that can be linked to your anonymous email account. ProtonMail offers apps for iOS and Android.
Threema. Threema is a secure messenger and can be used anonymously. Make end-to-end encrypted voice calls. Threema doesn’t use a phone number as unique identifier; instead, Threema issues a randomly generated ID.
OnionShare. OnionShare is an open source tool that lets you securely and anonymously share a file of any size. It works by starting a web server, making it accessible as a Tor onion service, and generating an unguessable URL to access and download the files. It doesn’t require a third-party file-sharing service.
CryptoStopper. CryptoStopper is ransomware detection software to stop actively-running ransomware infections on Windows workstations and servers. CryptoStopper also provides free tools to simulate a ransomware attack on your network to find out if your are protected. Plans start at $1 per month per machine.
Surveillance Self-Defense. Surveillance Self-Defense is a guide from Electronic Frontier Foundation to protect against electronic surveillance, for people all over the world. It includes step-by-step tutorials for installing and using a variety of privacy and security tools, but also aims to teach people how to think about online privacy and security even as the tools and adversaries change around them.
Random.org. This tool allows you to generate random passwords. The passwords generated by this form are transmitted to your browser securely, via SSL, and are not stored on the Random.org server.
Boxcryptor. Boxcryptor encrypts your sensitive files and folders in Dropbox, Google Drive, OneDrive, and many other cloud storages. It combines the benefits of the most user friendly cloud storage services with the highest security standards worldwide. Encrypt your data right on your device before syncing it to the cloud providers of your choice.
The Guardian Project. The Guardian Project creates secure apps, open-source software libraries, and customized mobile devices that can be used to protect communications and personal data from intrusion, interception, and monitoring. Its apps include a mobile browser, chat messenger, and camera.
Tails OS. Tails is a live operating system that you can start on almost any computer from a USB stick or a DVD. Use built-in and pre-configured cryptographic tools to encrypt your files, emails, instant messages, and more.
Online anti-malware scanners. Here is a useful list of anti-malware scanners, which includes VirSCAN, Jotti, Avast!, ThreatExpert, Eureka, and more.
File shredders. Typically, your deleted files remain on your computer until the space is overwritten by something else. File shredder programs overwrite selected files, so they can never be recovered. Here is a list of file shredders to remove your deleted files once and for all.
Cloudflare. Cloudflare Security Services protect and secure websites, applications, and APIs against denial-of-service attacks, customer data compromise, and abusive bots.
Symantec Small Business. Symantec offers a suite of solutions for small and mid-sized businesses. Tools include SSL-TLS certificates, Norton Shopping Guarantee with free protection for online shoppers, endpoint protection cloud, email protection, endpoint encryption, and a ghost solution suite.
Facebook Security Checkup. Use Facebook’s security checkup to review and add more security to your account. Learn how to protect your password, and get alerts when someone tries logging into your account from an unrecognized computer or mobile device.
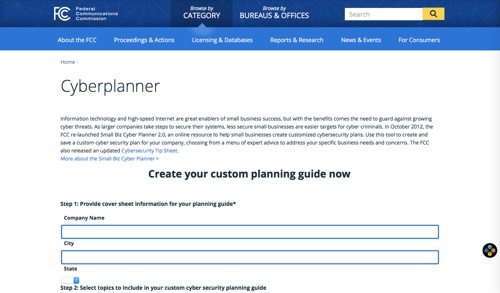
F.C.C. Cyber Planner. From the U.S. Federal Communications Commission, here is the Small Biz Cyber Planner 2.0, an online resource to help small businesses create customized cyber security plans. Use this tool to create and save a custom cyber security plan for your company, choosing from a menu of expert advice to address your specific business needs and concerns. The F.C.C. also provides a cyber security tip sheet.